GnuPG Public Key Infrastructure
Infrastructure Integration Support
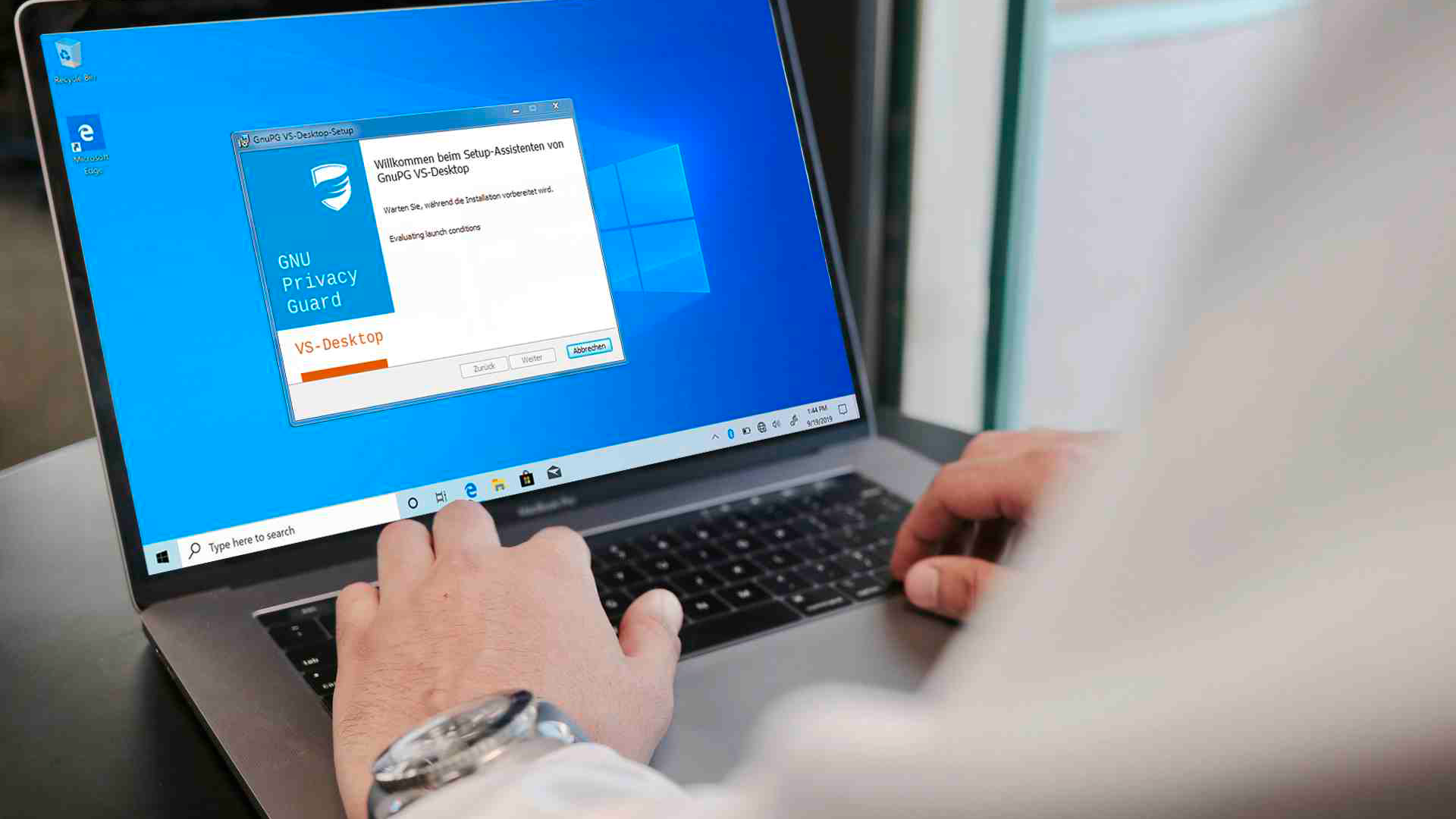
Choose both security and user-friendliness without compromise. We are dedicated to merging these elements seamlessly. Our solutions are designed to integrate effortlessly into your existing work environment. Once set up, your employees will instantly feel at ease in their familiar surroundings. Whether you're a small or large organization, GnuPG Desktop® and GnuPG VS-Desktop® flawlessly fit into any network infrastructure.
Distributing Keys/Certificates
Public keys do not require special protection or secrecy–the integrity and correctness of certificates are secured through authentication. Distributing certificates is also straightforward: you can publish them on a website, a network drive, or distribute them via email. The technical effort is minimal, but for a larger number of keys/certificates, this method can become cumbersome.
Therefore, we recommend automating distribution within an appropriate infrastructure. Our software is versatile and supports publishing keys and certificates on internal keyservers (LDAP, AD, LDS), Web Key Directory (WKD), Web Key Service (WKS), and through Kleopatra groups.
Our Enterprise packages for GnuPG VS-Desktop® and GnuPG Desktop® include support for integration into your infrastructure at no additional cost.
Certificate Management
There are various ways to automatically distribute authenticated certificates to users. We offer scalable solutions for secure trust management:
Simple and Efficient
Distributing Keys and Certificates
The management of OpenPGP and X.509 certificates can be handled by an internal key server. Directory services such as Active Directory Lightweight Directory Services (AD LDS) for Windows or OpenLDAP for Linux are suitable for this. To allow external communication partners access to your organization's certificates, set up a Web Key Directory (WKD)–this only requires a web server running under the domain-name of your email address.
Key Validation: Authentication
Our software can be used to map a hierarchical trust model with a higher-level Certification Authority (CA). In a small organization, one person or a group of people takes over the authentication management and thus the role of the Certificate Authority. With GnuPG actium, an automated authentication process for certificates is possible. It is also possible to prevent the authentication of certificates by users.
Administration
We provide a custom schema for the directory service you use. This allows, among other things, searching for certificates based on fingerprints, and storing information about subkeys and email addresses.
Our Services Explained
Implementation
As part of our Enterprise package for GnuPG VS-Desktop®, we offer comprehensive consulting services. We address your questions individually and discuss the optimal deployment of our solution with your technicians and experts. This includes equipping users with keys, deciding on the use of hardware tokens, providing necessary information for secure mail and data exchange, and creating a business continuity plan. Additionally, we answer your questions about end-to-end encryption.
Support
Should you face challenges with our software, you are not alone—we're here to help immediately! Are you unable to use a communication partner's key? Is a signature displayed as invalid? Do you suspect a bug in our software? We are a reliable point of contact for our customers. We are available by phone to offer advice and practical assistance and regularly provide software updates. This ensures that you are never left alone with any issues and receive direct, timely support from the manufacturer.
Optimization
The crypto engine GnuPG has been around since 1997. The foundation of our programs and tools is extremely flexible and versatile. Known as the Swiss Army knife of Crypto, it has numerous options, all described in our comprehensive manuals. We assist you with configuration and ensure that GnuPG Desktop® meets your specific requirements and integrates seamlessly into your operational workflow. Our goal: to provide you with a tailored solution that is both powerful and user-friendly.